The US Justice issued a response to the request for a review of the detention of Ilya Lichtenstein and Heather Morgan, accused of laundering money from the multi-million dollar hack of the bitcoin (BTC) exchange Bitfinex in 2016. They were denied parole and detailed details were revealed of what his criminal acts would have been.
In a release signed by the prosecutor Matthew Graves of the Court of Justice of the District of Columbia, the United States authorities explained why they consider it pertinent that the detainees remain in that condition. In addition, they provided more details about the arrest that occurred on Tuesday.
Regarding the first, the authorities think that The conditions that ensure that the couple will appear at the time of being judged are not met. One reason to believe this is that the defendants have a lot of money and false identities, so they could go on the run, and would even be encouraged to do so. In fact, it is believed that they had a contingency plan to emigrate to Russia or Ukraine before the Covid-19 pandemic.
Advertising
For these reasons, their request for parole was denied and they were ordered to remain in custody without bail. Meanwhile, more details of an investigation that has been going on for a long time and that would be giving results for the American Justice since January 2022 were published.
How to launder more than USD 1,000 million in bitcoin
As CriptoNoticias reported, Lichtenstein and Morgan They were arrested after one of the wallets was confiscated that they would have used to carry out “complex money laundering processes.”
The discovery of these keys, stored in an encrypted document in a cloud service that detailed addresses of more than 2,000 accounts, allowed the US government to take control of 94,000 BTC. That amount would be equivalent to approximately USD 4,129 million, according to the price of the cryptocurrency at the closing of this note.
For the legal representative of the government, there is “convincing evidence” that the funds seized from Lichtenstein come directly from the accounts used to house the funds stolen from Bitfinex. It is also detailed that Morgan would have played a central role in the money laundering network, although the defense of the accused wants to pretend otherwise.
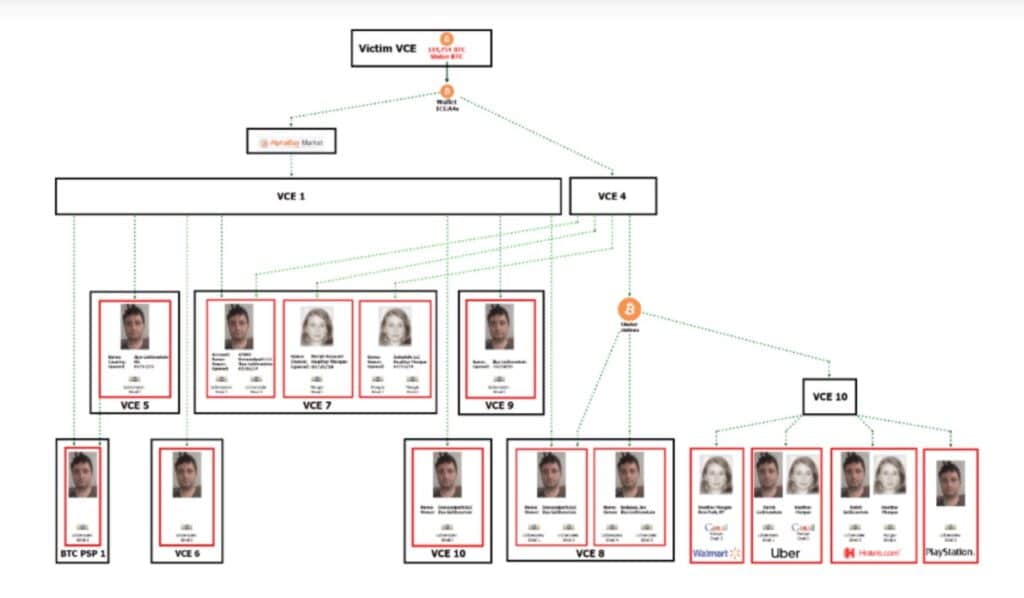
This money laundering scheme included an account in the Alphabay black market marketplace —closed in 2017—, other bitcoin wallets and also accounts on other platforms that, although not in the name of the accused couple, were related to them. This would have been verified from the data found in Lichtenstein’s cloud account, says the authorities’ letter.
Source: District of Columbia Court of Justice.
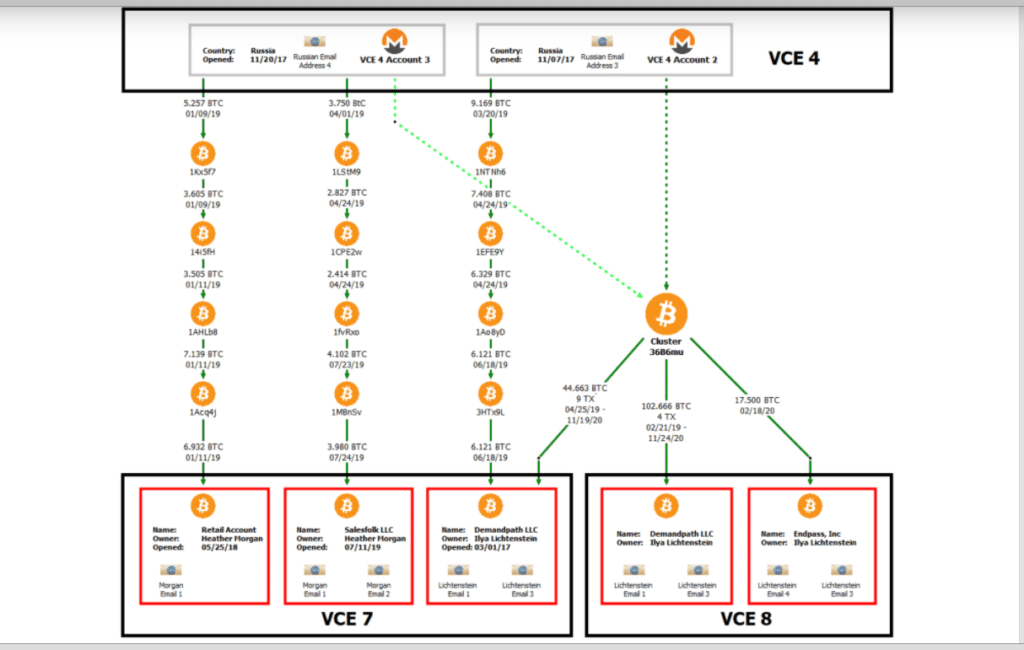
Morgan and Lichtenstein contradicted each other, according to the US Justice, when asked about some of the accounts seen in the graph above. For example, that happened with the VCE 7 account, allegedly related to a woman’s marketing company called Salesfork.
Heather Morgan claimed that this account It would be used to receive cryptocurrency payments from her clients and that the funds deposited there had been a gift from her husband in 2014. Until then, he maintained, he had kept them in a cold or hardware wallet. However, when tracking account activity, they found that this was not true, and that the funds actually came from multiple shipments from VCE 4.
Likewise, the Justice also revealed that it was able to intercept several communications – what type is not revealed – between the couple and their accountant. In these messages, the accountant requested details about the bitcoin operations they had carried out to file the corresponding tax return. However, Morgan would have responded with scant and unclear data, aware that “at most, we will owe a few taxes” if these were not enough.
Access to Lichtenstein’s account
The Justice statement also details how access was gained to Ilya Lichtenstein’s cloud account. This was accomplished by court order. Despite the fact that the files contained therein were strongly encrypted, the authorities were able to access several of them. That was how they got the addresses of the defendant’s wallets.
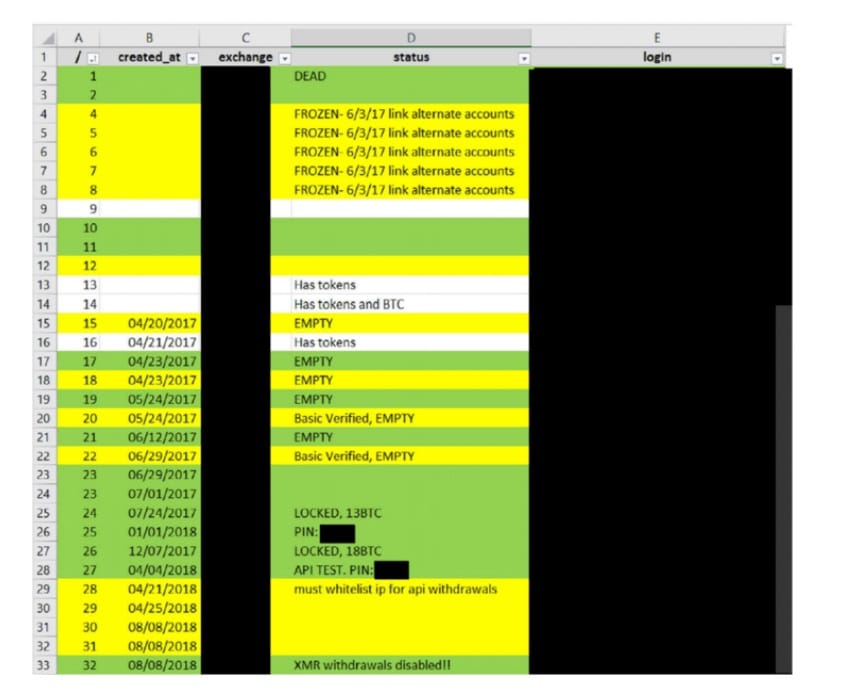
Source: District of Columbia Court of Justice.
However, the statement details several accounts still could not be seized. Some of them, it is said, include the word «dirty» (“dirty”) on your ID. For example, “dirty wallet» (“dirty purse”).
Also found in this account addresses of the dark web in which, apparently, false passports and identities are sold. It is thought that this is how the couple would have obtained their apocryphal documentation. There were also other subfolders that even contained profile photos to bypass exchanges’ KYC procedures.
Operations in Ukraine
In addition to all of the above, Lichtenstein and Morgan would have also had plans in Ukraine as of 2019. These, like those described above, are also related to money laundering.
For example, it was found in a folder personal data of many people from Ukraine that could have been used to create false documentation. In addition, there were supposed companies with which to operate for money laundering and lists of sellers and distributors available on the dark web.
Finally, other details of the first operation in the apartment of the couple in New York, carried out on January 5. One of them is that Morgan would have refused to hand over his cell phone, and the agents “had to take it out of his hands.”
Under the bed, the officers would have found a box with multiple cell phones, SIM cards and “various electronic devices”, some of them encrypted or password protected. However, no gold coins were found, which Lichtenstein is presumed to have bought from a “dealer” on the black market.


