Most antiviruses only scan RAM, so malware hidden in VRAM would be undetectable.
A tool for hide malware in the VRAM memory of the graphics card and run from there, it’s being sold on a dark web hacker forum.
Computers process data and run applications in the device’s RAM, commonly known as main memory.
But a modern computing device, use different types of memory. ROMs are read-only (some rewritable), and although there have been cases of infected ROMs, they are not used to run apps or store data in real time.
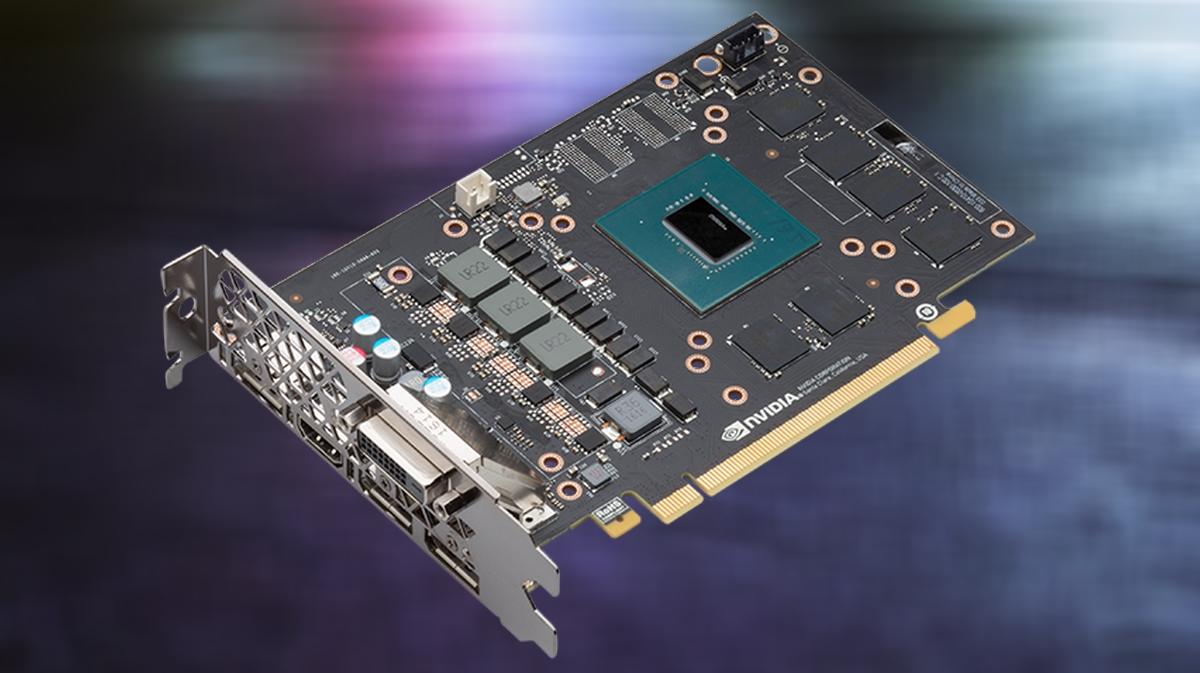
We also have VRAM memory, call graphics or video memory, because it is the one they use graphics cards and some laptops on their integrated GPUs.
This graphic memory is used to store the textures and data required by the video card when graphics are to be displayed on the screen.
From a technical point of view its function is similar to RAM memory, and in fact many laptops use RAM memory as video memory. But it is still difficult to run applications directly in VRAM memory.
However, as it counts Bleeping Computer, in a well-known hacker forum a tool is being sold to hide malware in the VRAM memory of graphics cards, and several copies have already been sold.
According to its creator, this tool works by reserving address space in the GPU memory buffer, and uses it to store malware and run it from there.
Tested to work with an AMD Radeon RX 5700 card, as well as the GeForce GTX 740M and GTX 1650 from NVIDIA. Also with Intel’s integrated UHD 620/630 GPUs.
The advantage of using this system for cyber criminals is that antiviruses only scan RAM, not VRAM. So the malware could be kept safe and avoid almost all antivirus.
It is not the first virus to work on the GPU. There have already been others, the most popular being JellyFish.
But according to its author, this new malware is more sophisticated and more undetectable, because it does not need to access the user’s workspace, where it could be detected.