Key facts:
140 ransomware strains were active during 2021.
The hackers ask for, in addition to bitcoins, monero (XMR) as payment to stop the attacks.
More than 600 million dollars (USD) in ransomware payments were recorded in 2021, an activity that grew remarkably and whose numbers may increase even more, since it is an underestimate of the blockchain analysis firm Chainalysis.
In a publication In its blog, the analytical company specified that the total amount in dollars for these attacks, which are defined as data kidnapping, may end up being much higher for the period that includes 2021, whose figure, for the moment, amounts to USD 602 millions. In fact, they estimate that the year just ended could be much bigger for ransomware.
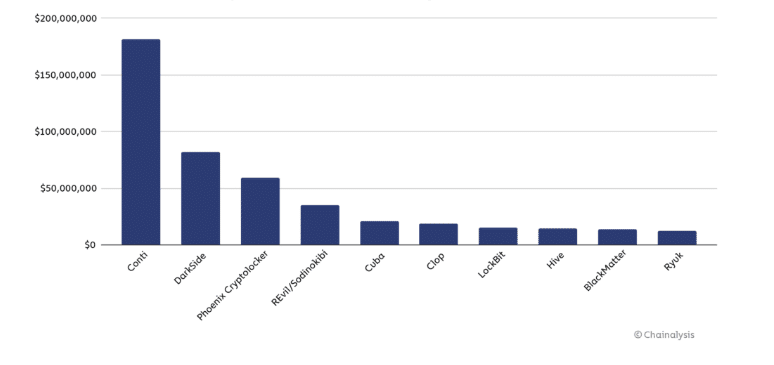
The firm maintains that, in 2021, Conti was the most used ransomware strain by hackers. They say that, with this virus, they extorted around USD 180 million from their victims.
Another strain with great activity was DarkSide, both for the total funds extorted, and for its leading role during the attack on the Colonial Pipeline, which was one of the most notable during 2021 and which caused fuel shortages in several US cities.
For Chainalysis, that attack is a reminder that ransomware is highly dangerous, because they often target critical infrastructure that keeps a country running.
140 strains of ransomware on the prowl
The firm highlights that, during 2021, at least 140 ransomware strains received payments from their victims. They compare with 2020, when 119 strains were active, and 2019, when 79 were involved in the attacks.
Those numbers are emblematic of the intense ransomware growth we’ve seen over the past two years. Most ransomware strains come and go in waves, staying active for a short period of time before going dormant.
Chainalysis report.
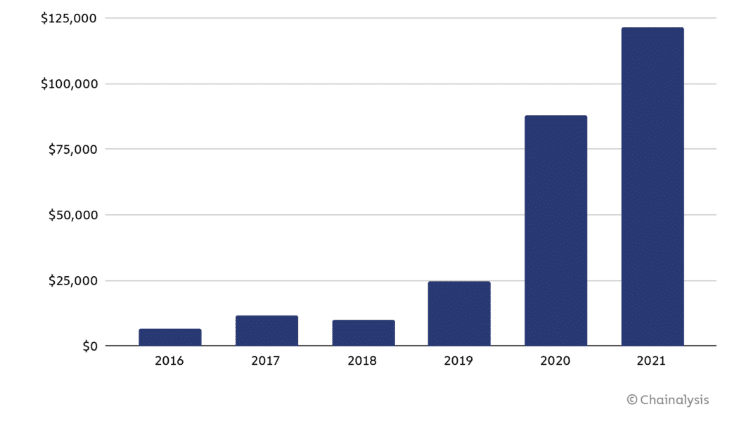
They also describe that the average size of ransomware payments in 2021 was USD 118 thousand, compared to USD 88 thousand in 2020 and USD 25 thousand in 2019. Record payouts of up to $40 million were received by the Phoenix Cryptolocker strain.
They explain that the increase in ransom amounts responds to the approach of hackers, who direct their attacks against large companies and organizations. A strategy that, according to the firm, “is enabled in part by the use made by ransomware attackers of tools provided by external providers to make their attacks more effective.”
Funds destined to improve their attacks
During the past year, 16% of the funds obtained from the attacks were used by hackers to obtain tools and services that increased their attacks. Likewise, they compare it with 2020, when 6% of the amount was used for the same purposes.
While some of that activity may constitute money laundering rather than the purchase of illicit services, we believe the increased use of those services is one reason ransomware attackers became more effective in 2021, as evidenced by the increase in the average payout size of victims.
Chainalysis, blockchain analysis firm.
Speaking about money laundering, they explained that most of the funds obtained by the ransomware strains were sent to centralized exchanges, such as Binance or Coinbase. They also highlighted high-risk exchanges, where there are fewer restrictions, “but they mostly incorporate exchanges with more established compliance programs”.
They also highlight that there was a significant amount of funds taken to mixers and other addresses that are commonly associated with other forms of illegal activities.
Name changes, a strategy of the attackers
Chainalysis referred to the average activity of ransomware strains that were typically active for at least two months in 2021. This was because they changed their name.
They explain that last year, ransomware attackers, after publicly stating that they would cease operations, appeared again shortly after, but with a different name. This was determined by similarities in the ransomware code.
“So while at least 140 ransomware strains were active in 2021, many of those strains were in fact run by the same cybercriminal groups,” the firm noted.
“These strains try to create the illusion that they belong to different cybercriminal organizations by creating separate victim pay sites and other infrastructure, but share similarities in their code,” he added.
For Chainalysis, ransomware, in addition to being dangerous, is also one of the most dynamic and constantly changing forms of crime related to cryptocurrencies. “Between constant rebranding, shifting money laundering strategies, and the influence of geopolitics, it’s hard to know what’s coming next.”
The size of ransomware payments has grown noticeably since 2016. / Source: Chainalysis.
Be careful with Monero
Chainalysis highlighted that a trend that should be taken into account is ransom payments with monero cryptocurrency. Analysts have seen that more and more attackers demand that victims pay with this cryptoactive, whose main characteristic is the anonymity it offers.
They explain that while most attackers continue to ask for bitcoin as payment, “cybersecurity professionals and law enforcement should be on the lookout for ransom notes requesting Monero.”
Or with assets associated with other protocols with privacy-enhancing features, as this will change the investigative tactics they must employ.


