The most popular SoCs on the market have a corrupted bluetooth that can be used by hackers to lock, freeze or take control of these devices. Some manufacturers have looked the other way.
In a connected world where we all have the same communication protocols, a widespread security breach puts us all at risk.
We already saw it with Meltdown and Specter at Intel It’s been a few years now, but you don’t have to look back and do too much memory to remember similar cases, unfortunately.
Of course, the case that concerns us today is serious, which unfortunately we will remember for a while.
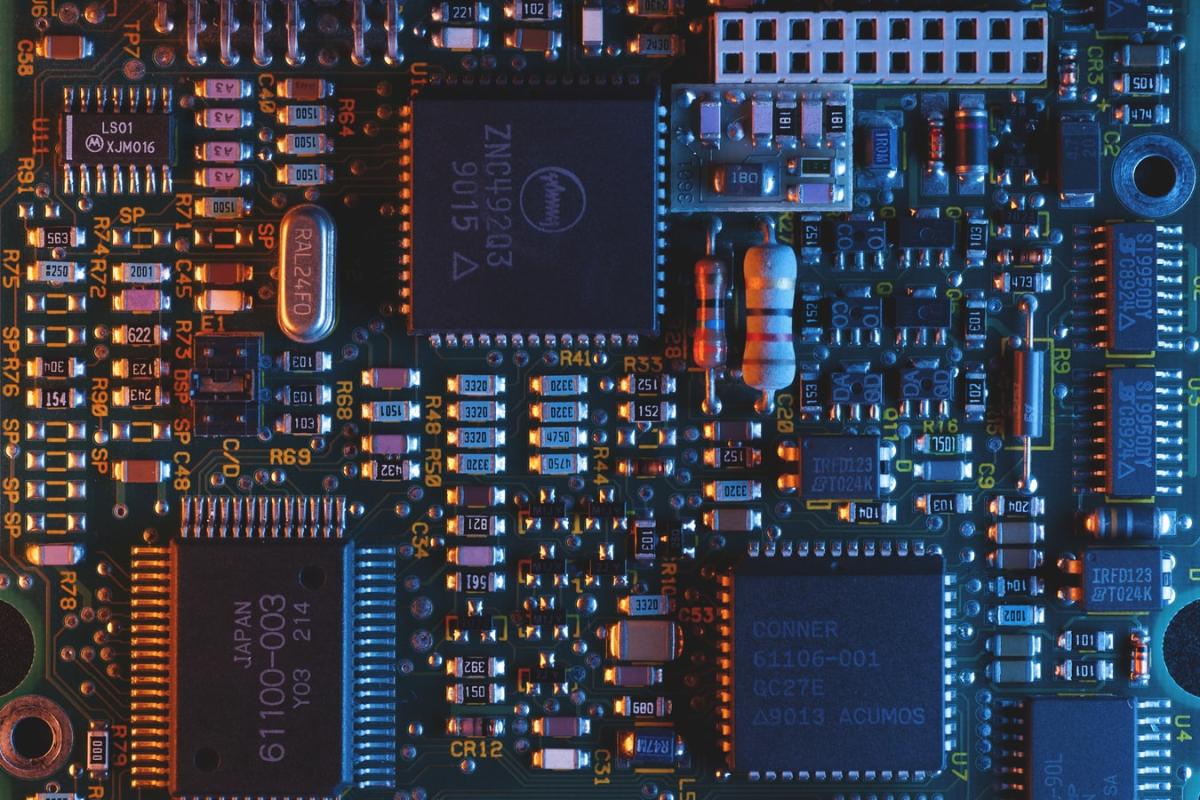
But what happened? A team of cybersecurity researchers this week released details on a set of 16 vulnerabilities affecting the Bluetooth software stack included in multi-vendor SoCs important.
The vulnerabilities, which have been called BrakTooth, allow attackers to lock and freeze devices or, in the worst case, execute malicious code and take control of entire systems.
Days after the investigation was published, security experts believe that the situation is even worse, since it is most likely that the same Bluetooth firmware is used within more than 1,400 chipsets.
Affecting a wide variety of devices, such as: laptops, smartphones, industrial equipment, cars and smart devices of the “Internet of things”.
It is believed that the number of affected devices is in the billions, but the impact of BrakTooth is different depending on the SoC board that the device mounts and the bluetooth software stack that it carries.
The worst vulnerability is CVE-2021-28139, which allows attackers to run their own corrupted code on vulnerable devices through Bluetooth LMP (Link Manager Protocol) packages in order to gain control of the device.
Research shows that Microsoft Surface laptops, laptops, and laptop computers are vulnerable to these attacks. Dell desktops and various smartphone models with Qualcomm SoC. As you can see, the scope is enormous.
The 11 vendors suffering from this security flaw were contacted months before the researchers released the research, and despite more than 90 days’ notice, only Espressif Systems, Infineon (formerly Cypress), and Bluetrum have released patches up to the date.
Texas Instruments, the chip giant, claimed that it would not address the failures that affected their products.
The extent of this huge security flaw remains to be seen, but if at the first change there are affected manufacturers who look the other way, the big losers will be us.